Network Segmentation Best Practices: Top Security & Microsegmentation Tips
Network segmentation best practices are essential for protecting your business from cyber threats and limiting the spread of attacks. By dividing your network into smaller, manageable parts, you can control access, improve monitoring, and reduce risks. In this blog, you’ll learn what network segmentation is, why it matters, and how to apply best practices for stronger network security. We’ll also cover security policies, firewalls, and how network segments help keep your data safe.
Understanding network segmentation best practices
Network segmentation best practices start with understanding how dividing your network into separate sections can limit the damage from cyber incidents. When you segment your network, you create barriers that stop attackers from moving freely if they get inside. This approach is especially important for businesses that handle sensitive data or use multiple devices and applications.
A flat network, where everything is connected without barriers, makes it easier for threats to spread. By using segmentation, you can apply different security policies to each part of your network. This means you can control who accesses what, making it harder for unauthorized users to reach critical systems. For example, you might separate your guest Wi-Fi from your business systems or use VLANs to keep departments apart.

Segmentation strategies: Avoiding common mistakes and pitfalls
It’s easy to overlook key details when setting up network segmentation. Here are some strategies to help you avoid the most common mistakes and keep your network secure.
Overlooking proper access control
Not setting clear access rules can leave your network open to unnecessary risks. Make sure each segment only allows access to those who truly need it. This limits the chance of internal or external threats moving between segments.
Ignoring regular updates to security policies
Security policies should be reviewed and updated often. If you forget to update them, your network segments might not be protected against new threats. Schedule regular reviews to keep your defenses strong.
Relying on a single firewall
Using just one firewall for all segments creates a single point of failure. Instead, place firewalls between key network segments to add extra layers of protection. This setup helps catch threats before they can spread.
Failing to monitor network traffic
Without proper monitoring, unusual activity can go unnoticed. Use tools that track traffic between segments. This helps you spot issues early and respond quickly.
Not separating sensitive data
Mixing sensitive data with general network traffic increases risk. Always keep critical information in its own segment. This makes it harder for attackers to access important files.
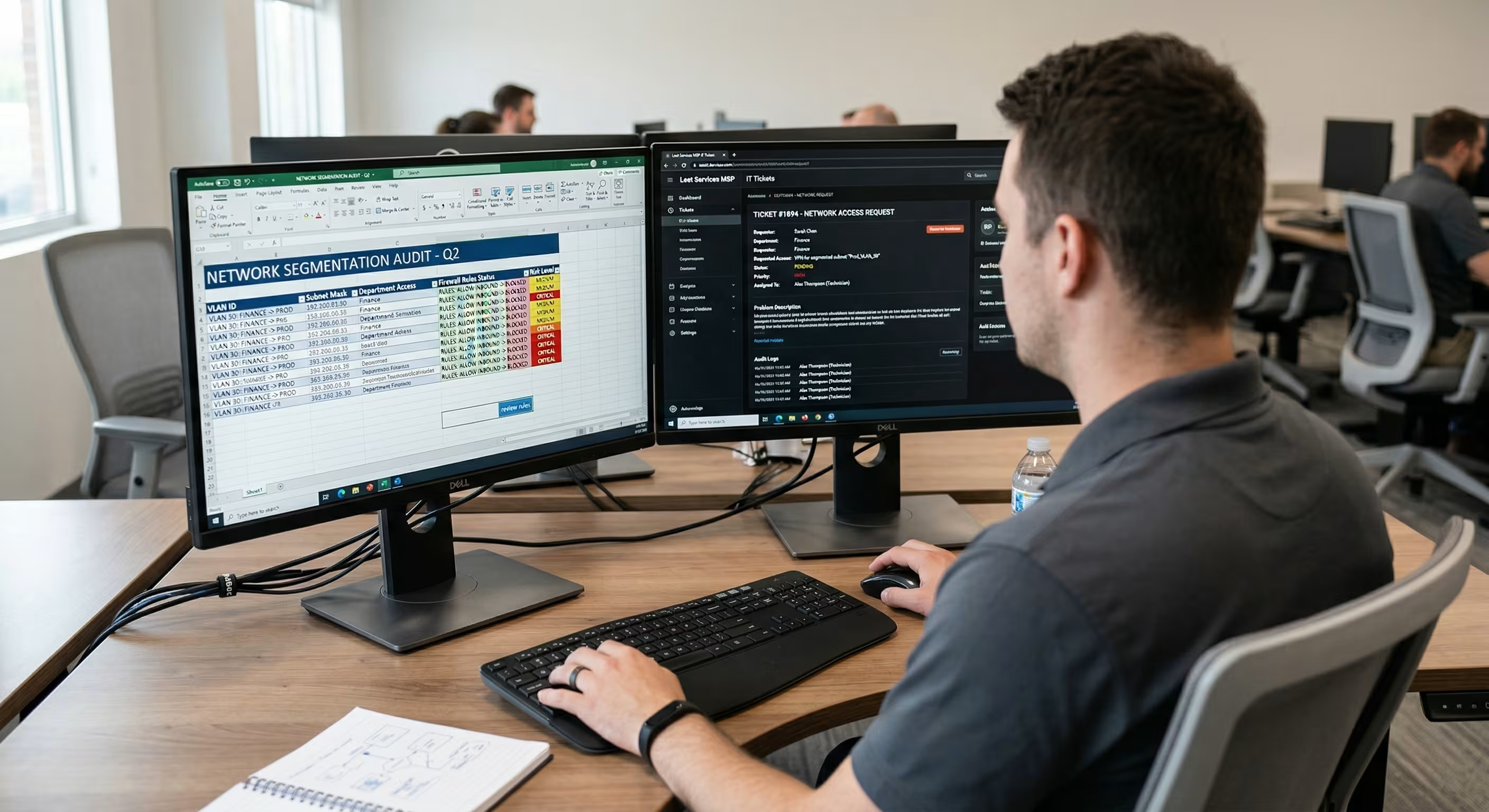
Skipping regular audits
Regular audits help you find weaknesses in your segmentation setup. Check your network segments and access controls at least once a year. Fix any gaps you find right away.
Poor documentation of network segments
If you don’t document your segmentation plan, it’s easy to lose track of what’s protected. Keep clear records of all segments, access rules, and changes. This makes troubleshooting and updates much easier.
Key benefits of segmenting your network
Segmenting your network has several important advantages:
- Limits the spread of cyber attacks by containing threats within one segment.
- Improves compliance with industry regulations by isolating sensitive data.
- Makes it easier to manage and monitor network traffic.
- Allows for tailored security policies for different departments or devices.
- Reduces the impact of human error by restricting access.
- Supports easier troubleshooting and faster response to incidents.

The role of microsegmentation in network security
Microsegmentation takes network segmentation best practices a step further by dividing your network into even smaller parts. This approach gives you more control over who can access each resource. It’s especially useful for businesses with cloud environments or many virtual machines.
With microsegmentation, you can apply security policies at a very detailed level. For example, you might allow a specific application to communicate only with certain servers. This reduces the risk of lateral movement if an attacker gets inside. Microsegmentation also helps you meet strict compliance requirements by limiting access to sensitive data.
Implementing microsegmentation does require careful planning. You’ll need to map out your applications, understand how they communicate, and set up rules that balance security with business needs. While it can be more complex than traditional segmentation, the added protection is often worth the effort.
Steps to implement network segmentation effectively
To get the most from network segmentation best practices, follow these steps:
Identify critical assets
Start by listing your most important data, systems, and applications. Knowing what needs the most protection helps you plan your segments.
Map network traffic flows
Understand how data moves between devices and departments. This helps you design segments that make sense for your business.
Define clear security policies
Set rules for who can access each segment and what they can do. Make sure these policies are easy to understand and enforce.
Use VLANs and routers for separation
Virtual LANs (VLANs) and routers help you physically and logically separate network segments. Use them to keep sensitive areas apart from general traffic.
Set up firewalls between segments
Place firewalls at key points to control traffic between segments. This adds extra layers of defense and helps block unauthorized access.
Monitor and audit regularly
Check your segmentation setup often. Use monitoring tools to track traffic and spot unusual activity. Audit your segments and access controls to find and fix any weaknesses.
Update documentation and train staff
Keep clear records of your segmentation plan and any changes. Make sure your team understands the rules and knows how to follow them.

Essential features of a strong segmentation plan
A strong segmentation plan should include:
- Clear identification of critical assets and data.
- Well-defined network segments based on business needs.
- Detailed security policies for each segment.
- Regular monitoring and auditing of traffic and access.
- Use of VLANs, routers, and firewalls for separation.
- Ongoing staff training and updated documentation.
Following these steps and features will help you apply segmenting network best practices and keep your business safe.
How Leet Services can help with network segmentation best practices
Are you a business with 15-80 employees looking to improve your network security? As your company grows, keeping your data safe and your systems running smoothly becomes even more important. Our team understands the unique challenges that come with scaling up and can help you apply network segmentation best practices tailored to your needs.
We specialize in designing, implementing, and maintaining secure network environments. If you want to reduce risks, meet compliance requirements, and protect your business from cyber threats, contact us today. Let Leet Services show you how effective segmentation can make a real difference for your business.
Frequently asked questions
What is network segmentation, and why does it matter?
Network segmentation is the process of dividing your network into smaller sections, called network segments. This helps control access and limits the spread of threats. By using segmentation, you can apply different security policies to each part, making it harder for attackers to move around.
A segmented network also makes it easier to monitor traffic and spot unusual activity. This approach is a key part of any strong cybersecurity plan and helps protect sensitive data.
How do I start implementing network segmentation in my business?
To implement network segmentation, begin by identifying your critical assets and mapping out how data moves in your network. Use VLANs and routers to separate different departments or device types. Place firewalls between segments to control traffic and block unauthorized access.
It’s important to set clear access control rules for each segment. Regularly review and update your segmentation plan to address new risks and business changes.
What are the main benefits of segmenting a flat network?
Segmenting a flat network helps contain cyber threats by stopping them from spreading across your entire system. It also allows you to apply specific security policies to each segment, improving your overall network security.
With proper segmentation, you can meet compliance requirements more easily and respond faster to incidents. This makes your IT environment safer and more manageable.
How does microsegmentation differ from traditional segmentation?
Microsegmentation goes beyond basic segmentation by dividing your network into even smaller parts. This lets you control access at a more detailed level, such as between individual applications or servers.
While traditional segmentation might separate departments, microsegmentation can isolate specific workloads. This approach is especially useful for businesses with cloud environments or strict compliance needs.
What security policies should I consider for each network segment?
Each network segment should have its own set of security policies based on what it contains. For example, sensitive data segments should have stricter access controls and monitoring.
You should also use firewalls and access control lists to limit who can enter each segment. Regularly review and update these policies to keep up with changing threats.
How often should I audit my network segments and access controls?
It’s best to audit your network segments and access controls at least once a year, or whenever you make major changes. Regular audits help you find and fix weaknesses before they become problems.
During an audit, check your documentation, review firewall rules, and test access controls. This process helps ensure your segmentation plan stays effective and up to date.





.avif)
.avif)
.avif)


